About
Password credentials are credentials composed of
- a password
It is something you know and is, therefore, a group identifier.
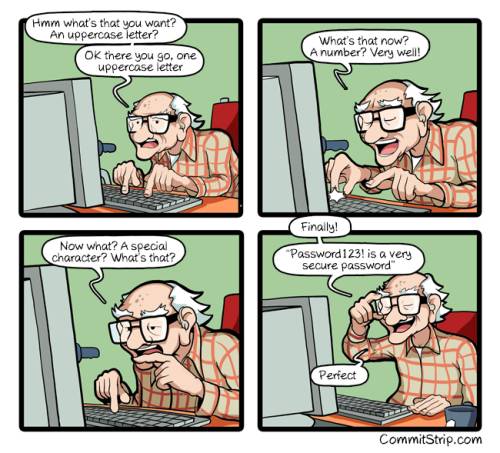
Het kostte me deze keer slechts 37 pogingen voor ik een wachtwoord bedacht dan aan alle regels voldeed.
How to send an 'E mail' - 1984
Password vs Cryptographic Key
| Password | Cryptographic Key | |
|---|---|---|
| multi-factor authentication context | something you know | something you have |
| Input | manual | automated (not meant to input manually) |
| Data Type | text | binary data |
| Complexity | Low | High |
| Memorization | Easy | Hard |
Passwords were created to be memorized by human beings (low-entropy) where a key were created to be use in automated process by computer. They are too complex and random to be memorized.
Passwords are text whereas cryptographic keys are binary data (even if serialized and deserialized as text via for instance base64) and are generally not meant to input manually.
In a multi-factor authentication context,
- passwords are something you know
- cryptographic keys are something you have.
Strategy
Password Storage
Any computer system that requires password authentication must contain a database of passwords, either hashed or in plaintext.
Because the tables are vulnerable to theft, storing the plaintext password is dangerous.
Most databases, therefore, store a cryptographic hash (ciphertext) of a user's password in the database 1)
In such a system, no one, including the authentication and admin system, can determine what a user's password is by merely looking at the value stored in the database.
Instead, when a user enters his or her password for authentication, it is encrypted (hashed), and that output is compared to the stored entry for that user (which was hashed before being saved). If the two hashes match, access is granted.
Two-way function
An encrypted copy of the password encrypted and unencrypted to plaintext for use with authentication methods such as Digest authentication.
The passwords are stored in encrypted form and they can only be decrypted by the application to provide access in authorized circumstances.
These protections, however, cannot prevent a malicious user with application access level from illicitly extracting them in the same manner that the application would do for legitimate use.
One-way hash function
When you just need to compare two passwords for authentication, you would use a one way hash function such as bcrypt.
These hashing functions are designed to always produce the same result from the same password input and to minimize collisions where two different passwords can produce the same result. This hash is always the same length and cannot be directly decrypted to reveal the plaintext password.
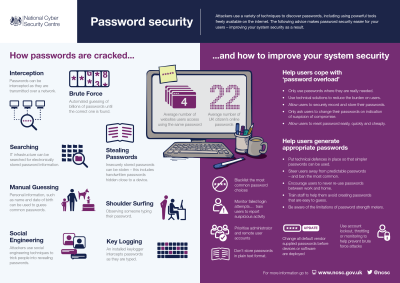
To protect against brute-force attacks, users who authenticate with passwords should set strong passwords or passphrases that include characters from multiple sets and are as long as the user can easily remember. See Password Technical Overview
Attack
To key
If you want to transform a password into an algorithmic key, you should use a KDF function.
Guided Navigation
Lib
- Java One Way: http://www.cs.umd.edu/~harry/jotp/
- Jenkins: secret
- Java from console. If an application needs to read a password or other secure data, it should use readPassword() or readPassword(String, Object…) and manually zero the returned character array after processing to minimize the lifetime of sensitive data in memory.
Console cons;
char[] passwd;
if ((cons = System.console()) != null &&
(passwd = cons.readPassword("[%s]", "Password:")) != null) {
...
java.util.Arrays.fill(passwd, ' ');
}
History
The MIT's Time-Sharing Computer is considered to be the first computer system to use passwords. https://www.wired.com/2012/01/computer-password/
Password Expiration
Standard
Documentation / Reference
- Password Hashing Competition. Password hashing is everywhere, from web services' credentials storage to mobile and desktop authentication or disk encryption systems. Yet there wasn't an established standard to fulfill the needs of modern applications and to best protect against attackers. We started the Password Hashing Competition (PHC) to solve this problem.