About
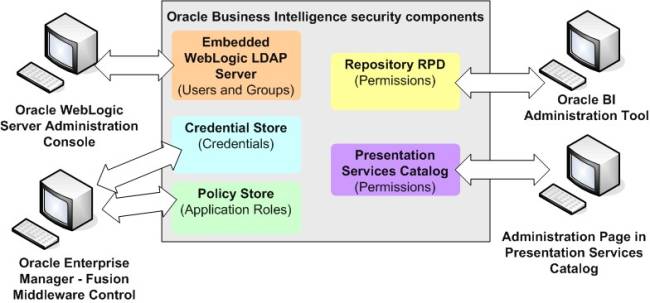
Oracle Business Intelligence uses a role-based access control model. Security is defined in terms of Application Roles that are mapped to directory server groups and users.
To define a complete security model, you have then to define:
- A security structure by creating this elements:
- The directory Server User and Group managed by the authentication provider.
- The application roles managed by the policy store provider
- a security_policy (permissions) split across the following components:
- Presentation Catalog
- Repository
- Policy Store to define the Application Policies managed by the policy store provider
The simplest way to set up security is to create Users and map them to the default Groups (that is, BIConsumers, BIAuthors, and BIAdministrators) that are installed out-of-the-box.
Articles Related
Security providers
A security provider is a security repository that you can call in order to get security information.
Any Oracle Business Intelligence installation makes use of the following types of security providers:
- authentication provider to authenticate
- policy store provider to give privileges on all application except for BI Presentation Servides (BI Server, BI Publisher, RTD,…)
- credential store provider to store credentials used internally by the BI application (such as Repository password, Proxy user between components,…)
Security Policy
In Oracle Business Intelligence release 11g, the security policy definition is split across the following components:
Presentation Catalog
This defines:
- the catalog objects
- and Oracle BI Presentation Services functionality
that the Users with specific Application Roles can access.
- Oracle BI Presentation Services Administration : Access to functionality is defined in the Managing Privileges page. Enables you to set privileges for users to access features and functions such as editing views and creating agents and prompts.
- Presentation Catalog privileges and access to presentation catalog objects is defined in the Permission dialog. In previous releases, you could assign permissions to objects from the Presentation Services Administration pages. In this release, you set permissions either in the Catalog Manager or the Catalog page of Presentation Services. The traverse option gives the possibility to the users to enter a path without having access to view/create content in intermediate folders.
.
Presentation Services does not have its own authentication system; it relies on the authentication system that it inherits from the Oracle BI Server. All users who sign in to Presentation Services are granted the AuthenticatedUser role and any other roles that they were assigned in Fusion Middleware Control.
When you assign permissions and privileges in Presentation Services, you can assign them in one of the following ways:
- To application roles — This is the recommended way of assigning permissions and privileges.
- To individual users — You can assign permissions and privileges to specific users, but such assignments can be more difficult to maintain.
- To Catalog groups — This approach is maintained for backward compatibility with previous releases only.
Repository
This defines which Application Roles and users have access to which items of metadata within the repository. The Oracle BI Administration Tool through the security manager is used to define this security policy.
Administration Tool enables you to perform the following tasks:
- Set permissions for business models, tables, columns, and subject areas.
- Specify database access for each user.
- Specify filters to limit the data accessible by users.
- Set authentication options.
Policy Store
The policy store through the application policies defines which Oracle BI Server, BI Publisher, and Real Time Decisions functionality can be accessed by given users or users with given Application Roles.